How to achieve a secure SSL encrypted transaction using an SSL certificate
Don’t think you need a safe SSL transaction on your website? Your customers are sure to disagree. After all, they’re not big fans of having their personal or financial information stolen by hackers through insecure websites. That’s why we’re here — to help you understand the importance of a secure SSL encrypted transaction.
Here’s what you need to know about SSL/TLS certificates and how they help you deliver a safe SSL transaction every time.
SSL Certificates: The Bedrock of Web Security
How many hours a day do you spend on your mobile phone or a computer? If you’re like an average American, it’d be somewhere around 8.5 hours. That’s a lot of time. Now, think about what you do for these hours. No, we’re not going to lecture you about your love for YouTube or your favorite web forum. We just want to ask what you do, that’s it.
Whether you’re scrolling through hundreds of cute cat photos or attending a video meeting, you’re doing one very important thing: exchanging information. In other words, you’re sending tons of data, and you’re receiving tons of data in return. That’s what you’re doing, technically speaking. And this is what an SSL/TLS certificate helps you to protect.
Save Up to 82% on SSL Certificates from RapidSSLonline!
Protect your website with an SSL Certificate from brands like RapidSSL, Symantec, GeoTrust, and Thawte.
SSL Secure Transaction: How to Protect Data in Transit
Whatever data you’re sending on the internet, how can you be so sure that someone won’t intercept and steal your data while it’s transmitting from your device to another? How can you be sure that nobody will take your credit card information while shopping online?
Well, that’s where SSL certificates come into play.
SSL, an acronym for “secure sockets layer,” is a protocol that secures the information while it’s in transit between two parties — namely, the client (your customer’s browser) and your web server (your website). In simpler words, it protects the information that you send/receive from access by unauthorized entities such as hackers. An SSL certificate, a digital file that’s installed on your web server, is what implements that secure SSL/TLS protocol on your website and fortifies the data that’s transmits between the two devices.
How do you identify an SSL-enabled website? Well, it’s quite easy. While browsing on the internet, you might have noticed that websites of some URLs start with HTTPS while some with HTTP. The “S,” which stands for “secure,” makes all the difference. It means that an SSL certificate is installed on the website. Once installed, all the data transmitting between your browser and server gets encrypted, and therefore, the data transaction between your device and server is secure.
While you’re sending your sensitive data on the internet, not only is encryption important but it’s also imperative to know who you’re communicating with. An SSL/TLS certificate plays a crucial role here. To get an SSL certificate, one must undergo a vetting process conducted by a certificate authority (CA). CA will only issue the certificate when it finds your website/organization to be genuine. In advanced SSL certificates such as OV and EV certificates, this process is quite stringent and is done manually to make sure of the organization’s legitimacy. Such vetting exists only with paid SSL certificate providers; the free SSL certificate providers lack the resources for it.
How SSL Works: Asymmetric Encryption
The fundamental function of an SSL certificate is to encrypt data. In simpler words, it turns the data into an undecipherable format so that no one can get to know what the original data was. And that’s what makes it almost impossible for cyber perpetrators to steal and/or tamper with the data.
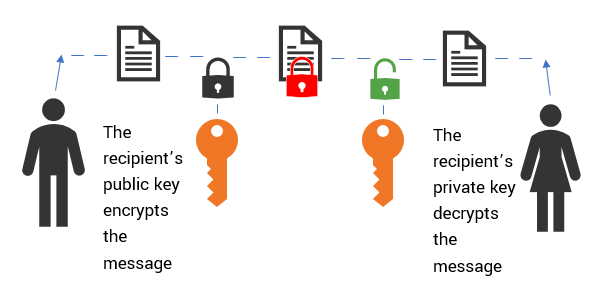
The data sent by the browser is encrypted using the public key, which is publicly available. When the data reaches the web server, it’s decrypted using the private key, which is stored securely on the web server. The data, for obvious reasons, can only be decrypted using the correlated private key. If you don’t have the private key, you cannot decrypt the data — it’s as simple as that.
The encryption method used by SSL is called asymmetric encryption or public key cryptography. This method involves two encryption keys: a public key and a private key. Both these keys are distinct but are also mathematically related to each other.
We’ve explained the entire process at a macro level, let’s try to understand it at a bit deeper level.
How an SSL Secure Transaction Works
An SSL Secure transaction is nothing but the interaction between your browser and the web server. This is how it works in a basic sense (without getting into the nitty-gritty of DNS requests and all that!):
- First, a site visitor’s browser requests a secure page.
- In response to this, the web server sends its public key with its certificate to the client (the end user’s web browser).
- Then, the browser validates the certificate and checks whether a trusted certificate authority (CA) issued it. It also checks the validity of the SSL certificate to ensure it isn’t revoked or expired.
- Once the certificate is validated, the browser then uses the public key to encrypt a random symmetric encryption key. (This symmetric key will be used to decrypt additional information in the next step.) The browser then sends the symmetric key, along with the encrypted URL required and other encrypted HTTP data, to the web server.
- In response, the web server decrypts the symmetric encryption key using its private key and then decrypts the URL and HTTP data using the symmetric key.
- After that, the web server sends back the requested HTML document and HTTP data that was encrypted with the symmetric key.
- Finally, the browser decrypts the HTTP data and HTML document using the symmetric key. This information is then displayed to the user.
That, in a nutshell, is how a secure SSL transaction works.
Final Word
If you want to secure your website using an SSL transaction, you just need to do one thing: install an SSL certificate. It’s as simple as that. However, you must do it sooner rather than later. After all, you don’t want to find out about your website’s security vulnerability from someone else by giving them a chance to take advantage of it!




