A political data analysis company has exposed 198 million US voter records
Chances are you’ve never heard of Deep Root Analytics, and in this case that may actually be a good thing. The fewer people that know of the GOP data analysis company—the lower the odds your voter records were compromised.
That’s because, according to security firm UpGuard, Deep Root Analytics left a database containing 198 million voter records exposed for the world to see.
To provide a little bit of context, according to US Census information there are approximately 200 million registered American voters. Carl wasn’t a math major, but 198 over 200 is… basically, ALL the voter records.
An UpGuard Cyber Risk analyst named Chris Vickery, who found the files, notified federal authorities who we can only assume wrote a sternly worded letter or some other bureaucratic foolishness.
What? I Read It for the Articles!
A Deep Root spokesman told the celebrity gossip blog, Huffington Post, “we take full responsibility for this situation.”
Deep Root also said that it believes only Vickery accessed the information, which is a lot like when you come home after a hard day’s work, open your son’s bedroom door to say hello and catch him trying to stuff an old Playboy under his mattress. Then when you ask him about it he tells you he only looked at it the one time.
You know, the one time you caught him.
I’m not saying I don’t believe Deep Root Analytics, I’m just—well, actually, yes that is what I’m saying. I don’t believe Deep Root.
Deep Rooted Analysis of Your Personal Information
What’s more frightening than the fact that your personal information – names, addresses, political affiliations – was potentially just compromised by a group whom you never even consented to having possession of your data in the first place?
How about the analysis they were performing on that questionably obtained information?
Vickery downloaded over 1.1 terabytes of unsecured information. What he found was staggering, Deep Root uses 9.5 billion (with a B) data points to build a terrifyingly accurate model of 198-million US voters’ political preferences using advanced algorithmic modeling across 48 political issues.
Not only does Deep Root have an obscene amount of data about you – data you never even agreed to let it have – that data has been used to profile you and segment you into demographics.
Ok, How Deep Are We Talking Here?
DEEP. Without getting overly political, there was even more valuable data on both the 2008 and 2012 elections available on those servers. This information is potentially way more dangerous than your voter records.
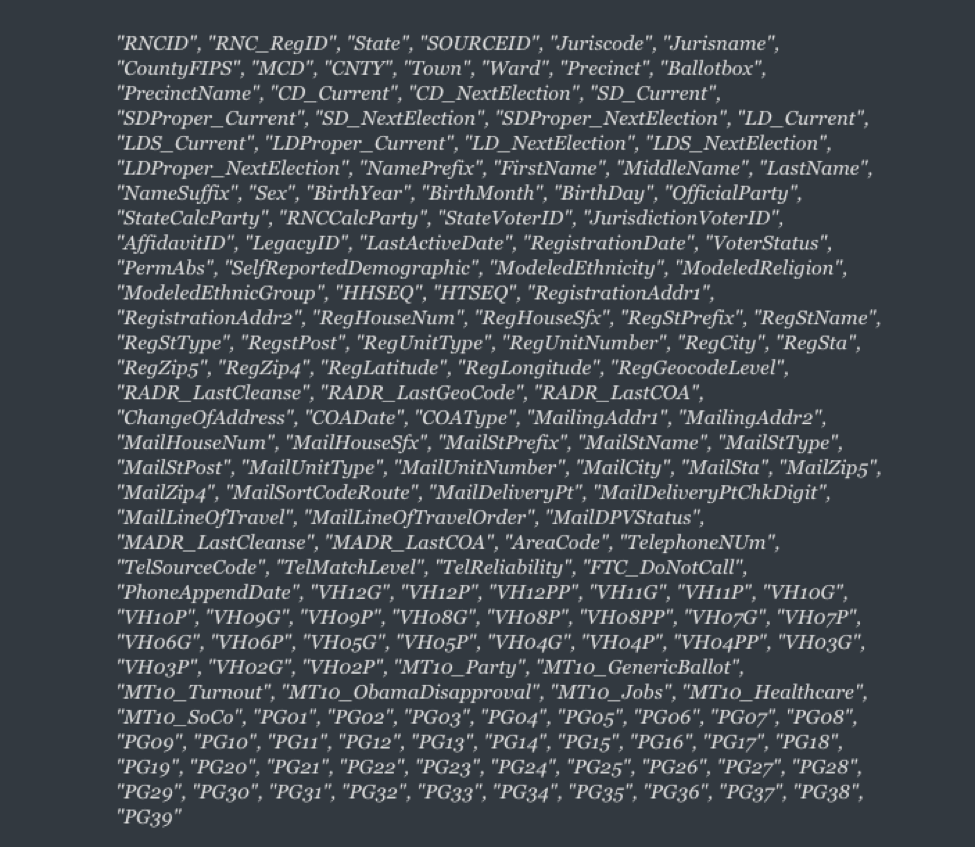
This is information from DataTrust, the “GOP’s exclusive data provider.” There are two sets of 51 files, one for each state and the District of Columbia. Each file, which is in .CSV form, contains 32-character RNC IDs – one for every voter in the database, regardless of affiliation – that link a number of data points together.
The IDs can be used to look up voters by name. For a frame of reference, here is a list of all the .CSV categories:
For those who don’t want to parse all of that, these data sets include things like: date of birth, addresses, phone numbers, party affiliations, racial demographics, religious leanings, registration status, income information—even if someone is on the federal “Do Not Call” list.
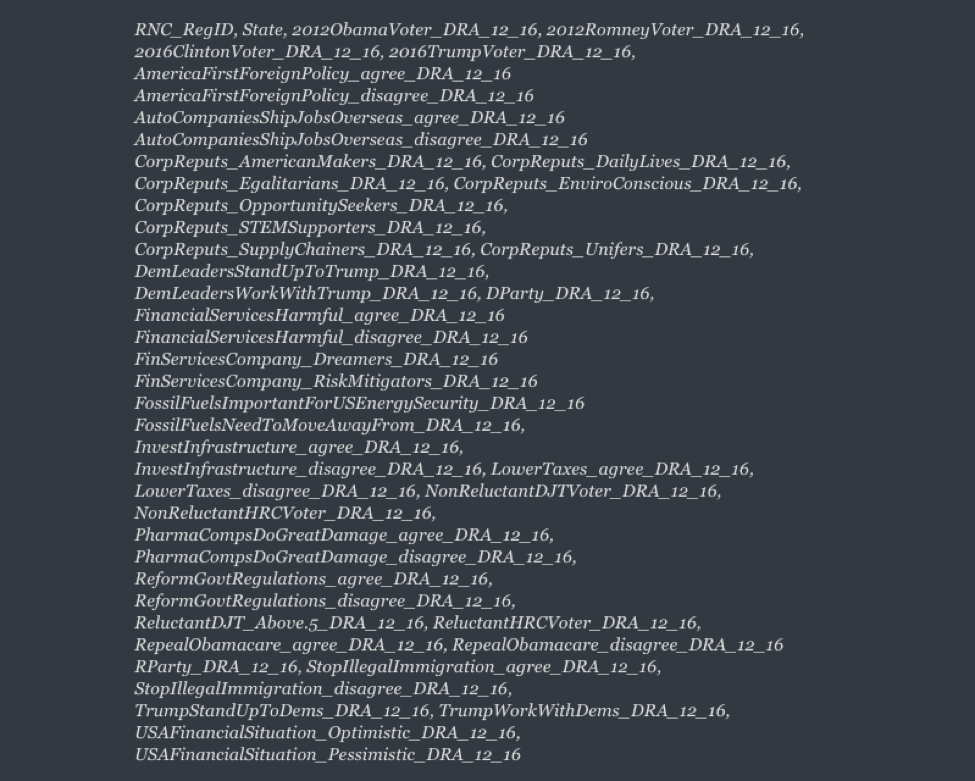
That data appears to have been used by another GOP analytics group, TargetPoint, to create a model for the 2016 election.
In a 50GB file, each potential voter is scored against 46 columns, each of which contains a policy or candidate that the voter may or may not be likely to vote for. The GOP then uses this information for micro-targeting (both parties do this, it’s not as if the GOP are the only ones performing this analysis).
Here’s a look at the issues you’re being modeled on:
Per Dan O’Sullivan, who wrote the UpGuard report and looked himself up: “It is a testament both to their talents, and to the real danger of this exposure, that the results were astoundingly accurate.”
When I read that last quote, I got so scared a little bit of pee came out. That’s a terrifying amount of information. And all that data was exposed online for who knows how long.
But it’s OK, Deep Root believes the only one who accessed it during that time is the guy who reported it.
How reassuring.
Stay cautious, my friends.